How Herman Miller Fell Vulnerable To XSS
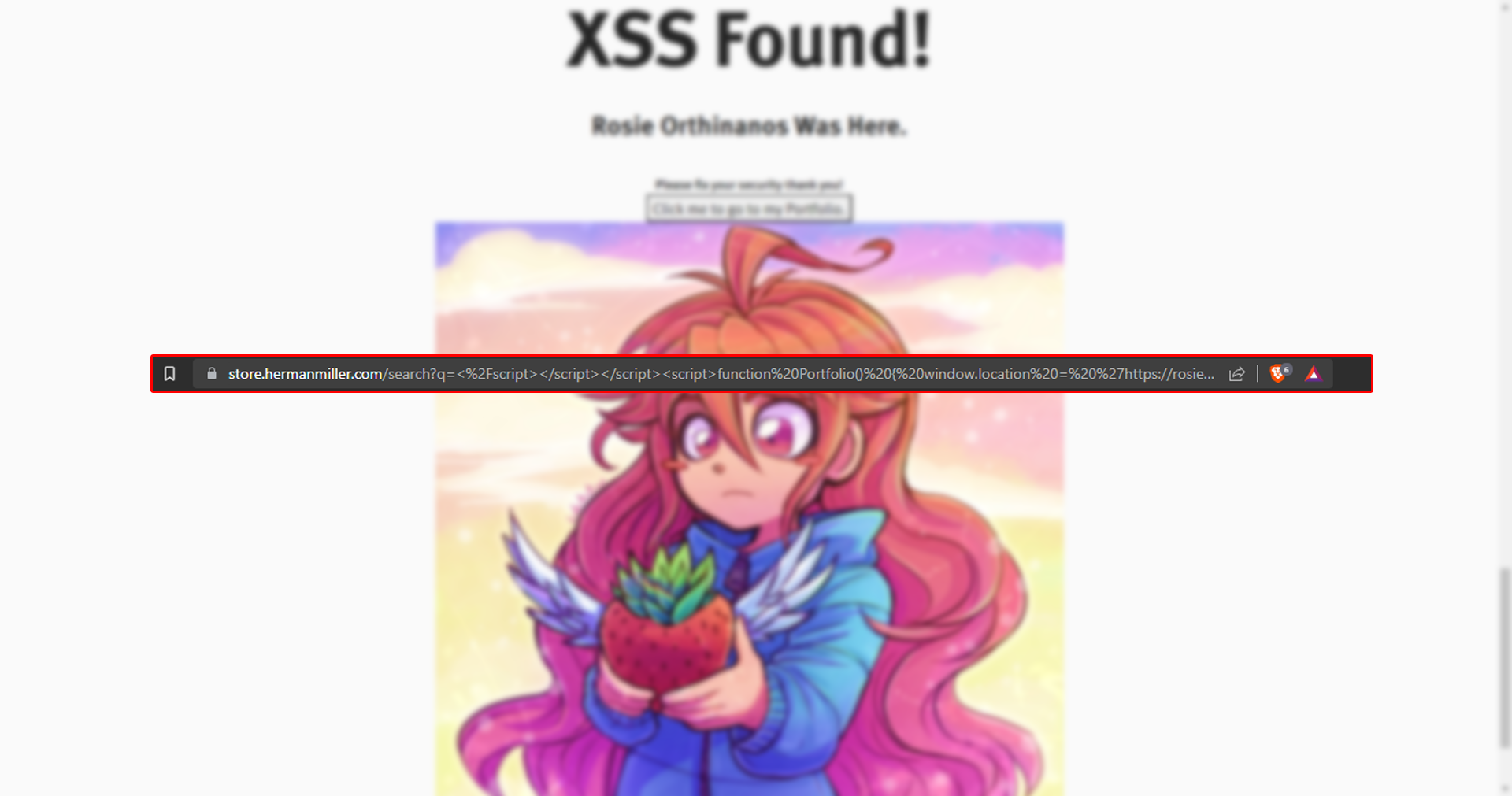
Table of Contents
What is Herman Miller
Herman Miller, is an American company that produces office furniture, equipment, and home furnishings. It's best known designs include the Aeron chair, Noguchi table, Marshmallow sofa, Mirra chair, and the Eames Lounge Chair. Herman Miller is also credited with the 1968 invention of the office cubicle (originally known as the "Action Office")
The Vulnerability
As of 06/07/2023 this vulnerability works but will most likely be fixed in the coming days.
- The query string
'trackPageView'which handles analytics & tracking doesn't get escaped, Allowing an attacker to inject arbitrary JavaScript code into the website. - Normally the code that handles
'trackPageView'will call to another function with your data for their analytics, But when attempting to'etmc.push'the data, it seems to corrupt and send a bunch of null strings instead.
When submitting </script><script>alert('hyia :)')</script> Herman Miller
would take that unescaped string and submit it to 'trackPageView', But because it gets
exeucted
it
completely corrupts your call to the analytics and not only executes the code allowing XSS, but the code
you submit within
the
'trackPageView' query within 'trackPage' completely null's the
query server side.
POC
To reproduce this vulnerability as of 06/07/2023
Start by going to Herman Miller. Once the
webpage has loaded
input this into the search bar
</script><script>alert(document.domain)</script>
once entered it will input the query into the trackPageView and execute it on the client
without escaping the
string. You can also click
here. to see it for yourself!
Like i previously mentioned though, This vulnerability will be fixed in the
coming
days most likely.
Summary
Personally i think that all companies should start checking their analytics & tracking for XSS,
due to this being the second time now that analytics has led to XSS.
I wrote a blog previously about how i discovered an unescaped string inside of Shopify's
'web-pixel-manger-setup' Which led to Dom-Based XSS if you'd like to read it you can Click Here!